NotificationThis report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise. This document is marked TLP:CLEAR--Disclosure is not limited. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp. SummaryDescriptionThis submission included one unique file. This file has been identified as a variant of the malware known as ICONICSTEALER. This variant of malware was utilized in the supply chain attack on the commercial software 3CXDesktopApp. The primary purpose of this malware is to steal sensitive data from a victim user's web browser, and make it available for exfiltration by a separate malicious component. Download the PDF version of this report: Submitted Files (1)e2ef455e92b3cb5a4c0f3093191d0bfb4fe3ff961e2a403feaa26060a298c70f (infostealer.dll) Findingse2ef455e92b3cb5a4c0f3093191d0bfb4fe3ff961e2a403feaa26060a298c70fTagsbackdoor information-stealer trojan Details
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis file is a 64-bit Windows DLL (Dynamic-link Library). Analysis indicates this application was part of a supply chain attack against the commercial application 3CXDesktopApp. This malicious DLL was included within an installer for the 3CXDesktopApp. The primary purpose of this DLL is to steal information from various web browsers employed by a victim user. This malware is being referred to in open source as ICONICSTEALER. During runtime the application first attempts to read a file named "\\3CXDesktopApp\\config.json". Additionally, the malware attempts to collect the victim system's hostname, domain name, and OS version (Figure 1). The malicious application next attempts to steal sensitive information from the victim user's web browser. Specifically it will target the Chrome, Edge, Brave, or Firefox browsers (Figure 2). It uses an embedded SQLITE library to query the browser databases for sensitive information (Figure 3). Analysis indicates the data stolen from the web browsers will be websites recently visited including sensitive parameters passed to the sites. These parameters could include sensitive information including login credentials or credit card numbers. No exfiltration capability was discovered within this malicious application, indicating it works with another malicious component to exfiltrate collected data. Screenshots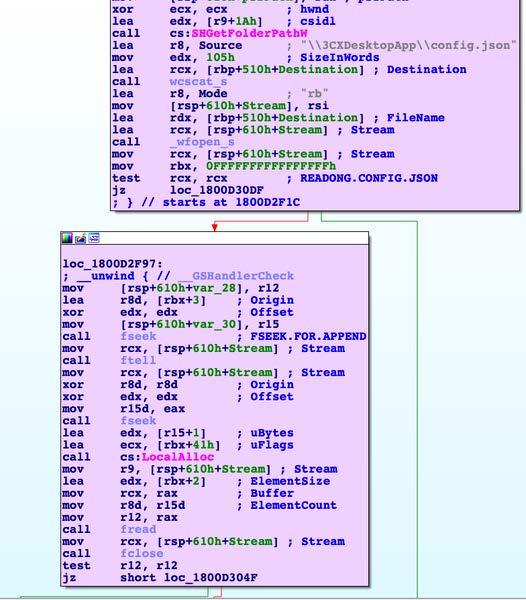 Figure 1 - This screenshot illustrates this malware attempting to access the file \\3CXDesktopApp\\config.json. 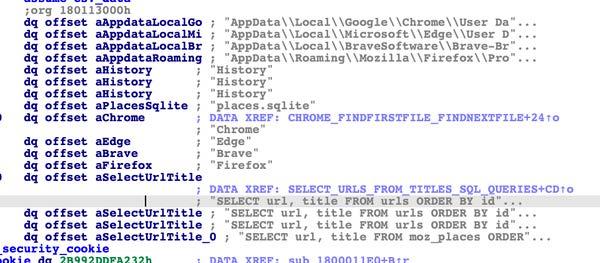 Figure 2 - This screenshot illustrates web browsers targeted by this malware, known as ICONICSTEALER. 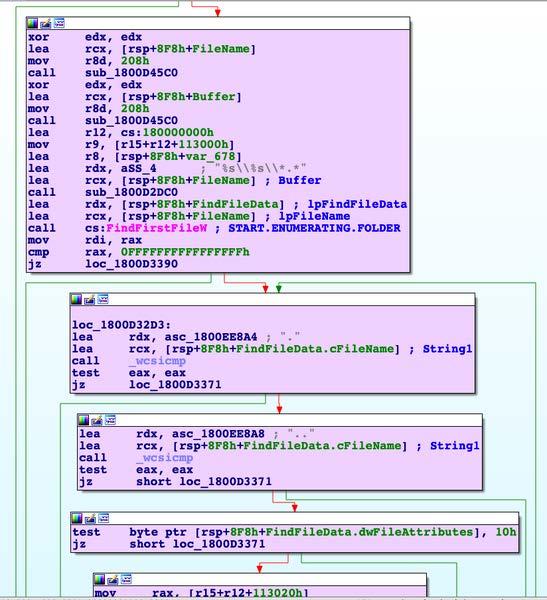 Figure 3 - This screenshot illustrates the malware beginning to search through folders of various web browsers looking for the database files. The database files will be queried with an embedded SQLITE library looking for sensitive information. 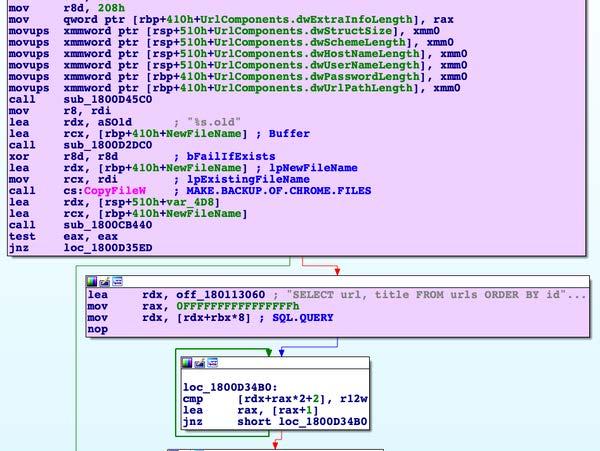 Figure 4 - This screenshot indicates the malware "backs up" the web browser databases before querying them for sensitive information. It may do this to prevent accidental corruption of the databases, or to prevent the browser from crashing if the user is currently browsing the web. RecommendationsCISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops". Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/ Document FAQWhat is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk. Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov. This product is provided subject to this Notification and this Privacy & Use policy. ACKNOWLEDGEMENTSSentinelOne contributed to this report. |
https://www.cisa.gov/news-events/analysis-reports/ar23-110a
NotificationThis report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise. This document is marked TLP:CLEAR--Disclosure is not limited. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be distributed without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp. SummaryDescriptionThis submission included one unique file. This file has been identified as a variant of the malware known as ICONICSTEALER. This variant of malware was utilized in the supply chain attack on the commercial software 3CXDesktopApp. The primary purpose of this malware is to steal sensitive data from a victim user's web browser, and make it available for exfiltration by a separate malicious component. Download the PDF version of this report: Submitted Files (1)e2ef455e92b3cb5a4c0f3093191d0bfb4fe3ff961e2a403feaa26060a298c70f (infostealer.dll) Findingse2ef455e92b3cb5a4c0f3093191d0bfb4fe3ff961e2a403feaa26060a298c70fTagsbackdoor information-stealer trojan Details
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis file is a 64-bit Windows DLL (Dynamic-link Library). Analysis indicates this application was part of a supply chain attack against the commercial application 3CXDesktopApp. This malicious DLL was included within an installer for the 3CXDesktopApp. The primary purpose of this DLL is to steal information from various web browsers employed by a victim user. This malware is being referred to in open source as ICONICSTEALER. During runtime the application first attempts to read a file named "\\3CXDesktopApp\\config.json". Additionally, the malware attempts to collect the victim system's hostname, domain name, and OS version (Figure 1). The malicious application next attempts to steal sensitive information from the victim user's web browser. Specifically it will target the Chrome, Edge, Brave, or Firefox browsers (Figure 2). It uses an embedded SQLITE library to query the browser databases for sensitive information (Figure 3). Analysis indicates the data stolen from the web browsers will be websites recently visited including sensitive parameters passed to the sites. These parameters could include sensitive information including login credentials or credit card numbers. No exfiltration capability was discovered within this malicious application, indicating it works with another malicious component to exfiltrate collected data. Screenshots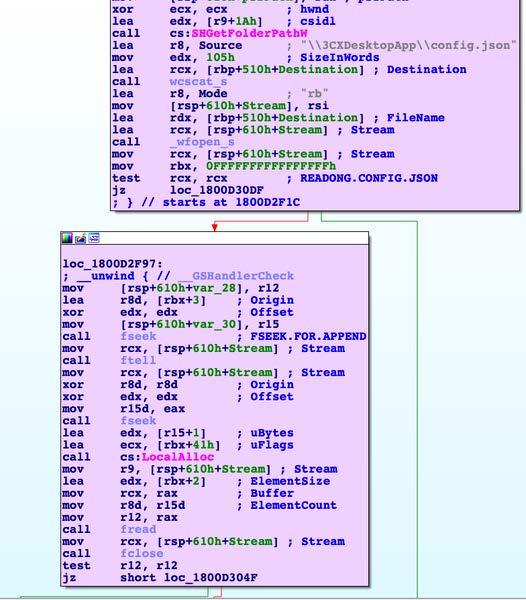 Figure 1 - This screenshot illustrates this malware attempting to access the file \\3CXDesktopApp\\config.json. 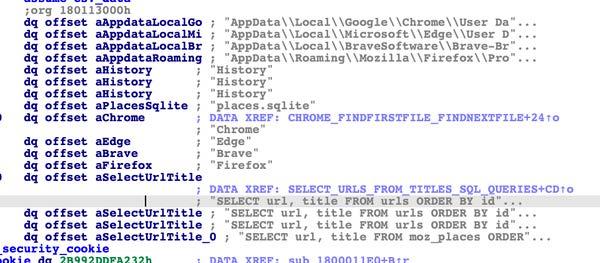 Figure 2 - This screenshot illustrates web browsers targeted by this malware, known as ICONICSTEALER. 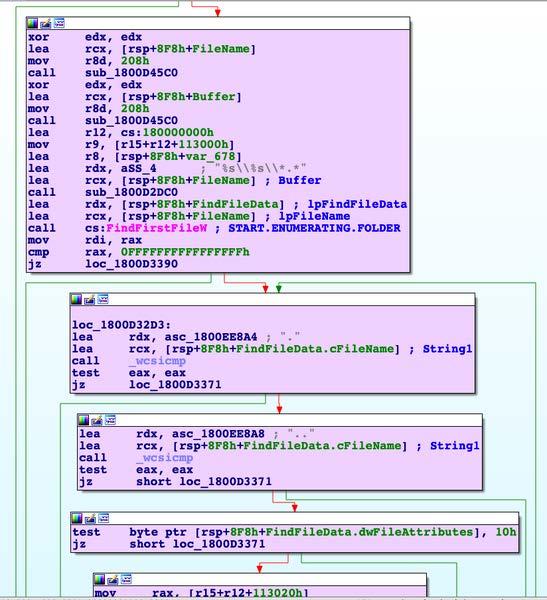 Figure 3 - This screenshot illustrates the malware beginning to search through folders of various web browsers looking for the database files. The database files will be queried with an embedded SQLITE library looking for sensitive information. 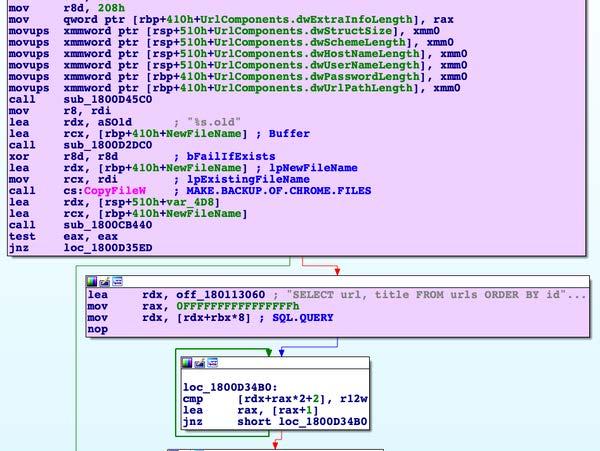 Figure 4 - This screenshot indicates the malware "backs up" the web browser databases before querying them for sensitive information. It may do this to prevent accidental corruption of the databases, or to prevent the browser from crashing if the user is currently browsing the web. RecommendationsCISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops". Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/ Document FAQWhat is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk. Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov. This product is provided subject to this Notification and this Privacy & Use policy. ACKNOWLEDGEMENTSSentinelOne contributed to this report. |
Source: CISA Analysis
Source Link: https://www.cisa.gov/news-events/analysis-reports/ar23-110a