NotificationThis report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise. This document is marked TLP:CLEAR--Recipients may share this information without restriction. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be shared without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp. SummaryDescriptionCISA obtained four malware samples - including SEASPY and WHIRLPOOL backdoors. The device was compromised by threat actors exploiting CVE-2023-2868, a former zero-day vulnerability affecting versions 5.1.3.001-9.2.0.006 of Barracuda Email Security Gateway (ESG). SEASPY is a persistent and passive backdoor that masquerades as a legitimate Barracuda service “BarracudaMailService” that allows the threat actors to execute arbitrary commands on the ESG appliance. WHIRLPOOL is a backdoor that establishes a Transport Layer Security (TLS) reverse shell to the Command-and-Control (C2) server. For information about related malware, specifically information on the initial exploit payload, a second SEASPY backdoor variant, and the SUBMARINE backdoor, see CISA Alert: CISA Releases Malware Analysis Reports on Barracuda Backdoors. Download the PDF version of this report: For a downloadable copy of IOCs associated with this MAR in JSON format, see: Submitted Files (4)29a41174eb9a39e0ad712ed5063c561e9c2e1db1f8f6b04b2ca369a6efc3ac9b (QuoVadis_Root_CA_1_G3.pem) 3f26a13f023ad0dcd7f2aa4e7771bba74910ee227b4b36ff72edc5f07336f115 (BarracudaMailService.old) 83ca636253fd1eb898b244855838e2281f257bbe8ead428b69528fc50b60ae9c (rverify) 9bb7addd96f99a29658aca9800b66046823c5ef0755e29012983db6f06a999cf (resize_reisertab) Findings3f26a13f023ad0dcd7f2aa4e7771bba74910ee227b4b36ff72edc5f07336f115Tagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. Relationships
DescriptionThis artifact is a 64-bit Executable and Linkable Format (ELF) file that has been identified as a "SEASPY" malware variant installed as a system service. The malware is a persistent backdoor that masquerades as a legitimate Barracuda Networks service. The malware is designed to listen to commands received from the Threat Actor's (TA's) C2 through TCP packets. When executed, the malware uses libpcap sniffer to monitor traffic for a magic packet on TCP port 25 (Simple Mail Transfer Protocol (SMTP)) and TCP port 587. It checks the network packet captured for a hard-coded string "oXmp". When the right sequence of packets is captured, it establishes a TCP reverse shell to the TA's C2 server for further exploitation. This allows the TA to execute arbitrary commands on the compromised system. The malware is based on an open-source backdoor program named "cd00r" and it is executed using the parameter below: --Begin argument-- 29a41174eb9a39e0ad712ed5063c561e9c2e1db1f8f6b04b2ca369a6efc3ac9bDetails-->
AntivirusNo matches found. YARA Rules
ssdeep MatchesNo matches found. Relationships
DescriptionThis artifact is an initialization script. Upon its execution it sets terminal settings to default using the 'stty sane' command. It then runs through the process of setting a runlevel variable and stops other services that were started by a previous runlevel. It also kills any services that are running on the current runlevel. Next, the script will start its associated services at the current runlevel. After logging functionalities are started, the script will then check if the runlevel is 3, which will result in the terminal screen being cleared using /usr/bin/clear. Finally, the script contains the command “/sbin/BarracudaMailService eth0” at the end. BarracudaMailService will be started automatically when the initialization script is run on the network interface eth0. BarracudaMailService is a known name for the SEASPY backdoor. Screenshots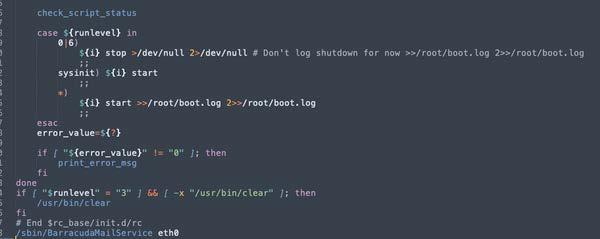
Figure 1. - At the end of the script the string "/sbin/BarracudaMailService eth0" is specified. 9bb7addd96f99a29658aca9800b66046823c5ef0755e29012983db6f06a999cfTagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis artifact is a 64-bit ELF file that has been identified as a "SEASPY" malware variant installed as a system service. This variant of SEASPY has had its symbols stripped. The malware is a persistent backdoor that masquerades as a legitimate Barracuda Networks service. The malware is designed to listen to commands received from the TA's C2 through TCP packets. When executed, the malware uses libpcap sniffer to monitor traffic for a magic packet on TCP port 25 (SMTP) and TCP port 587. It checks the network packet captured for a hard-coded string "TfuZ". When the right sequence of packets is captured this SEASPY variant launches an authentication sequence prior to launching the reverse shell. Once the TA authenticates, the malware starts a reverse shell on the infected system. This allows the TA to execute arbitrary commands on the compromised system. The malware is based on an open-source backdoor program named "cd00r" and it is executed using the parameter below: --Begin argument-- 83ca636253fd1eb898b244855838e2281f257bbe8ead428b69528fc50b60ae9cTagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis artifact is a 32-bit ELF file that has been identified as a malware variant named "WHIRLPOOL". The malware takes two arguments (C2 IP and port number) from a module to establish a Transport Layer Security (TLS) reverse shell. The module that passes the arguments was not available for analysis. Relationship Summary
RecommendationsCISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops". Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/ Document FAQWhat is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk. Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov. |
https://www.cisa.gov/news-events/analysis-reports/ar23-221a
NotificationThis report is provided "as is" for informational purposes only. The Department of Homeland Security (DHS) does not provide any warranties of any kind regarding any information contained herein. The DHS does not endorse any commercial product or service referenced in this bulletin or otherwise. This document is marked TLP:CLEAR--Recipients may share this information without restriction. Sources may use TLP:CLEAR when information carries minimal or no foreseeable risk of misuse, in accordance with applicable rules and procedures for public release. Subject to standard copyright rules, TLP:CLEAR information may be shared without restriction. For more information on the Traffic Light Protocol (TLP), see http://www.cisa.gov/tlp. SummaryDescriptionCISA obtained four malware samples - including SEASPY and WHIRLPOOL backdoors. The device was compromised by threat actors exploiting CVE-2023-2868, a former zero-day vulnerability affecting versions 5.1.3.001-9.2.0.006 of Barracuda Email Security Gateway (ESG). SEASPY is a persistent and passive backdoor that masquerades as a legitimate Barracuda service “BarracudaMailService” that allows the threat actors to execute arbitrary commands on the ESG appliance. WHIRLPOOL is a backdoor that establishes a Transport Layer Security (TLS) reverse shell to the Command-and-Control (C2) server. For information about related malware, specifically information on the initial exploit payload, a second SEASPY backdoor variant, and the SUBMARINE backdoor, see CISA Alert: CISA Releases Malware Analysis Reports on Barracuda Backdoors. Download the PDF version of this report: For a downloadable copy of IOCs associated with this MAR in JSON format, see: Submitted Files (4)29a41174eb9a39e0ad712ed5063c561e9c2e1db1f8f6b04b2ca369a6efc3ac9b (QuoVadis_Root_CA_1_G3.pem) 3f26a13f023ad0dcd7f2aa4e7771bba74910ee227b4b36ff72edc5f07336f115 (BarracudaMailService.old) 83ca636253fd1eb898b244855838e2281f257bbe8ead428b69528fc50b60ae9c (rverify) 9bb7addd96f99a29658aca9800b66046823c5ef0755e29012983db6f06a999cf (resize_reisertab) Findings3f26a13f023ad0dcd7f2aa4e7771bba74910ee227b4b36ff72edc5f07336f115Tagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. Relationships
DescriptionThis artifact is a 64-bit Executable and Linkable Format (ELF) file that has been identified as a "SEASPY" malware variant installed as a system service. The malware is a persistent backdoor that masquerades as a legitimate Barracuda Networks service. The malware is designed to listen to commands received from the Threat Actor's (TA's) C2 through TCP packets. When executed, the malware uses libpcap sniffer to monitor traffic for a magic packet on TCP port 25 (Simple Mail Transfer Protocol (SMTP)) and TCP port 587. It checks the network packet captured for a hard-coded string "oXmp". When the right sequence of packets is captured, it establishes a TCP reverse shell to the TA's C2 server for further exploitation. This allows the TA to execute arbitrary commands on the compromised system. The malware is based on an open-source backdoor program named "cd00r" and it is executed using the parameter below: --Begin argument-- 29a41174eb9a39e0ad712ed5063c561e9c2e1db1f8f6b04b2ca369a6efc3ac9bDetails-->
AntivirusNo matches found. YARA Rules
ssdeep MatchesNo matches found. Relationships
DescriptionThis artifact is an initialization script. Upon its execution it sets terminal settings to default using the 'stty sane' command. It then runs through the process of setting a runlevel variable and stops other services that were started by a previous runlevel. It also kills any services that are running on the current runlevel. Next, the script will start its associated services at the current runlevel. After logging functionalities are started, the script will then check if the runlevel is 3, which will result in the terminal screen being cleared using /usr/bin/clear. Finally, the script contains the command “/sbin/BarracudaMailService eth0” at the end. BarracudaMailService will be started automatically when the initialization script is run on the network interface eth0. BarracudaMailService is a known name for the SEASPY backdoor. Screenshots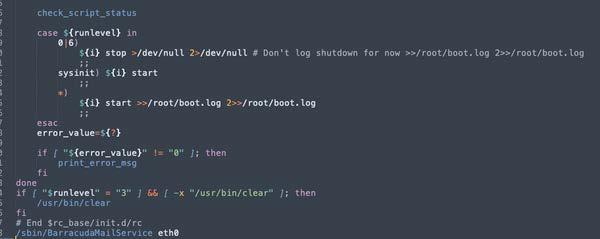
Figure 1. - At the end of the script the string "/sbin/BarracudaMailService eth0" is specified. 9bb7addd96f99a29658aca9800b66046823c5ef0755e29012983db6f06a999cfTagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis artifact is a 64-bit ELF file that has been identified as a "SEASPY" malware variant installed as a system service. This variant of SEASPY has had its symbols stripped. The malware is a persistent backdoor that masquerades as a legitimate Barracuda Networks service. The malware is designed to listen to commands received from the TA's C2 through TCP packets. When executed, the malware uses libpcap sniffer to monitor traffic for a magic packet on TCP port 25 (SMTP) and TCP port 587. It checks the network packet captured for a hard-coded string "TfuZ". When the right sequence of packets is captured this SEASPY variant launches an authentication sequence prior to launching the reverse shell. Once the TA authenticates, the malware starts a reverse shell on the infected system. This allows the TA to execute arbitrary commands on the compromised system. The malware is based on an open-source backdoor program named "cd00r" and it is executed using the parameter below: --Begin argument-- 83ca636253fd1eb898b244855838e2281f257bbe8ead428b69528fc50b60ae9cTagstrojan Details-->
Antivirus
YARA Rules
ssdeep MatchesNo matches found. DescriptionThis artifact is a 32-bit ELF file that has been identified as a malware variant named "WHIRLPOOL". The malware takes two arguments (C2 IP and port number) from a module to establish a Transport Layer Security (TLS) reverse shell. The module that passes the arguments was not available for analysis. Relationship Summary
RecommendationsCISA recommends that users and administrators consider using the following best practices to strengthen the security posture of their organization's systems. Any configuration changes should be reviewed by system owners and administrators prior to implementation to avoid unwanted impacts.
Additional information on malware incident prevention and handling can be found in National Institute of Standards and Technology (NIST) Special Publication 800-83, "Guide to Malware Incident Prevention & Handling for Desktops and Laptops". Contact Information
CISA continuously strives to improve its products and services. You can help by answering a very short series of questions about this product at the following URL: https://us-cert.cisa.gov/forms/feedback/ Document FAQWhat is a MIFR? A Malware Initial Findings Report (MIFR) is intended to provide organizations with malware analysis in a timely manner. In most instances this report will provide initial indicators for computer and network defense. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. What is a MAR? A Malware Analysis Report (MAR) is intended to provide organizations with more detailed malware analysis acquired via manual reverse engineering. To request additional analysis, please contact CISA and provide information regarding the level of desired analysis. Can I edit this document? This document is not to be edited in any way by recipients. All comments or questions related to this document should be directed to the CISA at 1-888-282-0870 or CISA Service Desk. Can I submit malware to CISA? Malware samples can be submitted via three methods:
CISA encourages you to report any suspicious activity, including cybersecurity incidents, possible malicious code, software vulnerabilities, and phishing-related scams. Reporting forms can be found on CISA's homepage at www.cisa.gov. |
Source: CISA Analysis
Source Link: https://www.cisa.gov/news-events/analysis-reports/ar23-221a