If product releases had a runway moment, Q1 at Rapid7 would’ve walked out in Cloud Dancer; crisp, confident, and quietly powerful, before breaking into a full gallop in the Year of the Horse. At Rapid7, our first-quarter launches combined velocity with refinement: meaningful enhancements designed to move security teams faster without adding complexity. Let’s cover off the key launches, one by one.
Detection and response
MDR for Microsoft
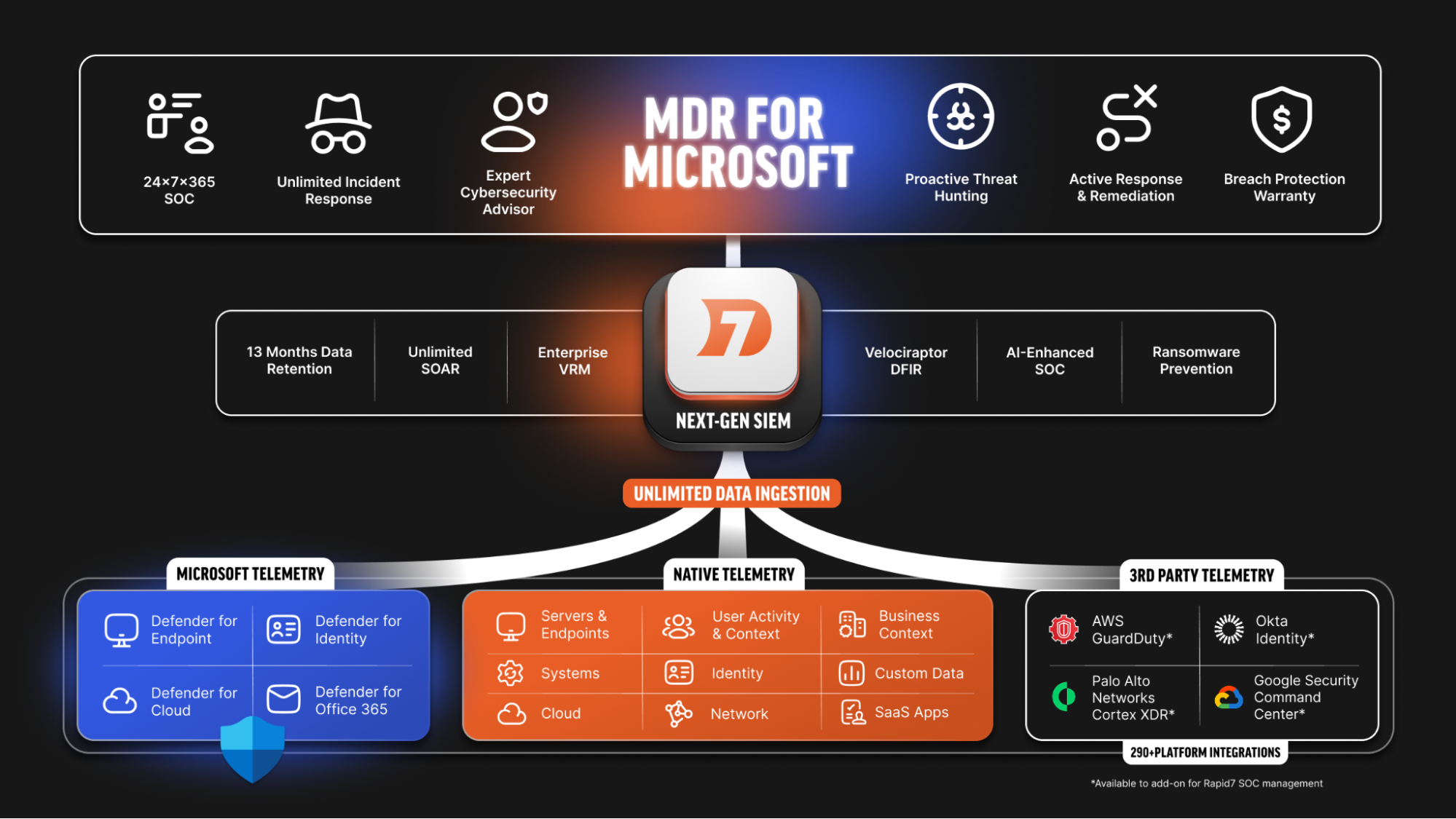
Getting more value from the tools you already have is an objective shared by all of us. For many of you, that translates to achieving greater security operations outcomes and resilience from your Microsoft technology. With MDR for Microsoft, organizations correlate their Microsoft, Rapid7, and third-party telemetry with prioritized risk context so the service can anticipate attacks before they start.
AI-powered triage and investigations – backed by unlimited incident response that ensures threats are fully eradicated – delivers certainty in an uncertain attack environment. Dedicated advisory provides strategic recommendations and program hardening guidance that drives long-term security resilience. Customers ultimately experience security operations excellence and achieve stronger outcomes from their existing Microsoft foundation.
Read the blog to learn more.
Rapid7 acquires Kenzo Security
The acquisition of Kenzo Security marks another step forward for the Rapid7 Command Platform and Rapid7’s vision for preemptive, AI-powered security operations. In an environment where most security teams are forced to leave large volumes of alerts uninvestigated, Kenzo’s agentic AI capabilities are expected to help accelerate Rapid7 from AI-assisted workflows toward AI-driven, machine-speed operations. Designed around specialized AI agents that work together across security operations tasks, this technology has the potential to reduce manual strain, broaden investigative coverage, and deliver more consistent, precise outcomes.
An average Kenzo customer reported a 94% reduction in investigation time, and their alert coverage increased from 12% to 100%. As these capabilities are brought into MDR, Managed Threat Complete, InsightIDR, and Incident Command, customers will benefit from a stronger, more scalable approach to cyber defense.
Incident Command
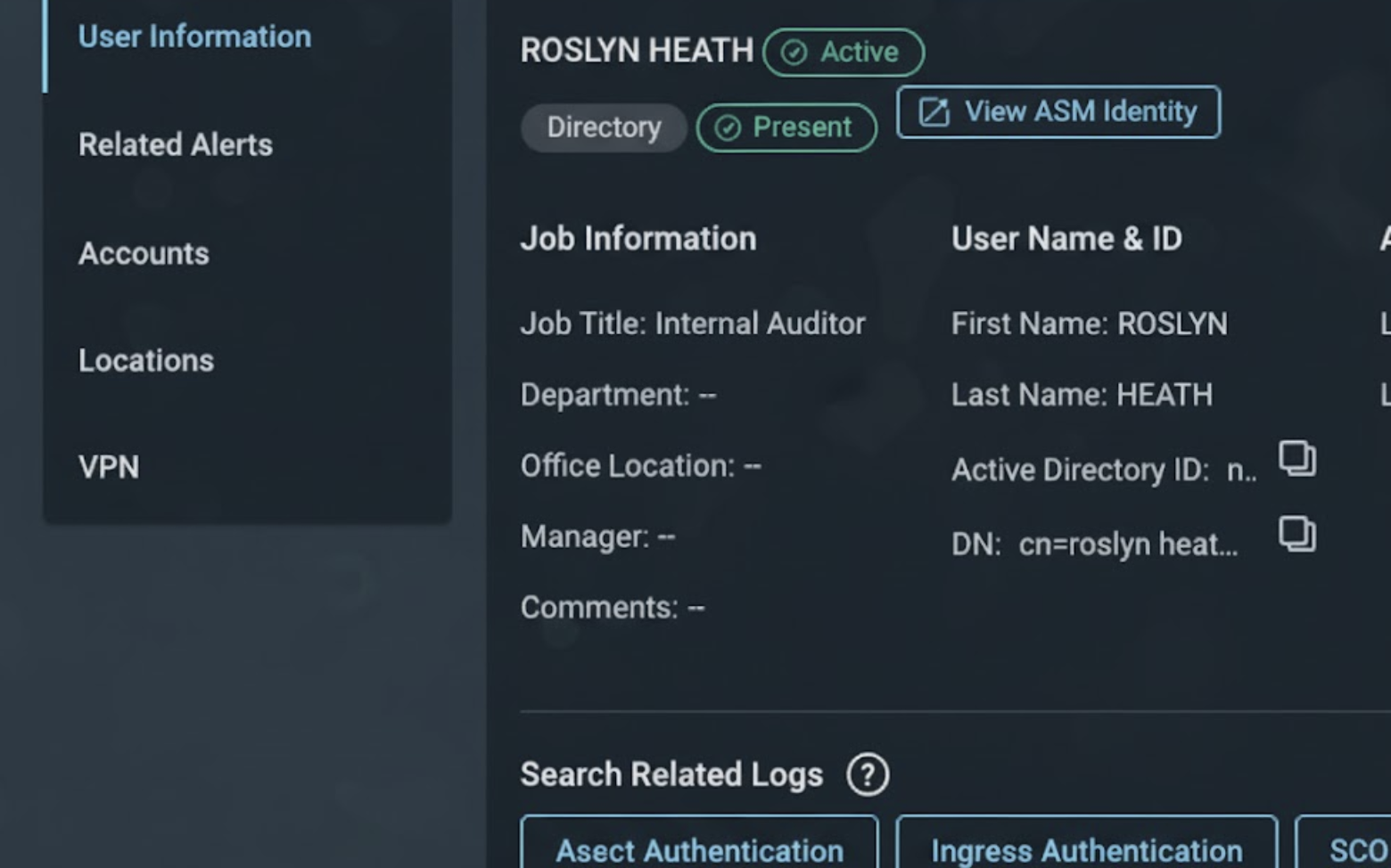
User to Identity mapping
Connecting user activity to full identity context is critical for faster, more confident investigations. With User to Identity mapping in Incident Command, analysts can seamlessly link SIEM users to their corresponding identity profiles, gaining instant visibility into MFA status, account posture, and group memberships. By unifying detection and exposure data, teams eliminate manual reconciliation and close visibility gaps across the identity attack surface. This enables faster triage, deeper insight into user risk, and a complete, connected view of identity-driven threats.
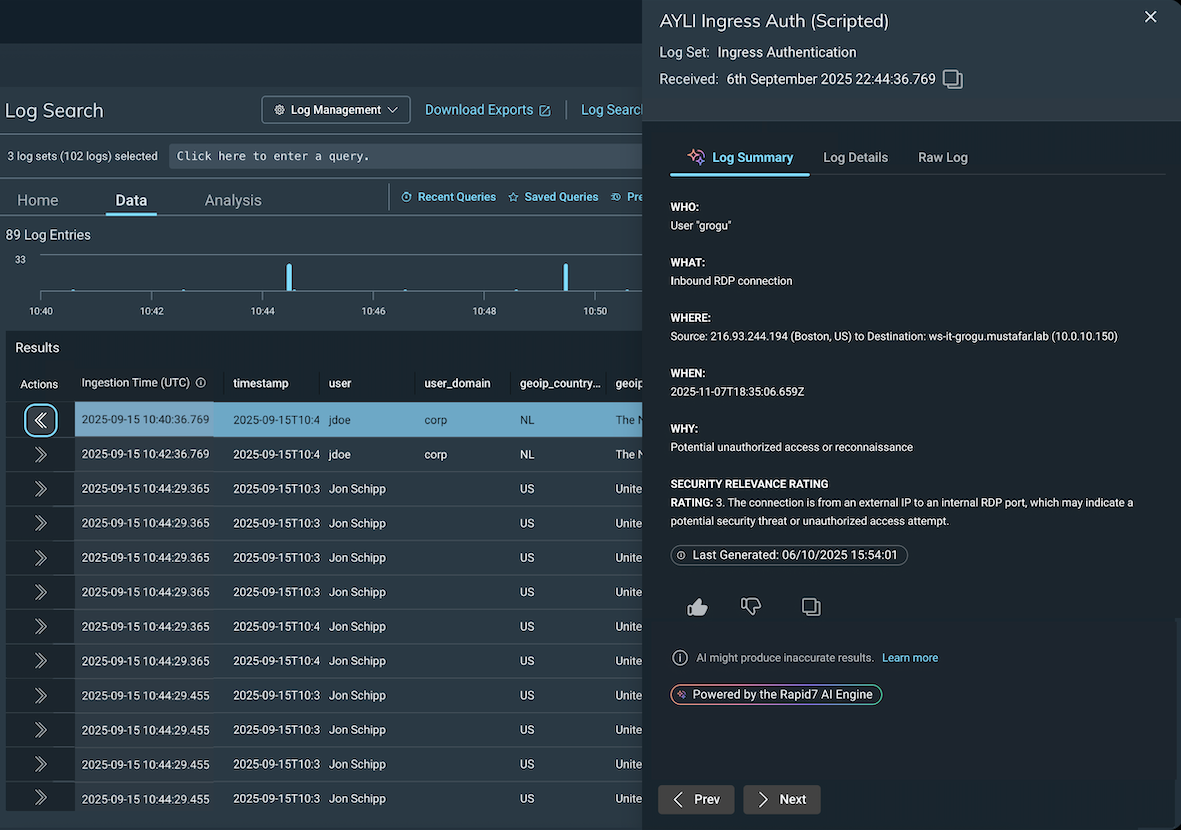
AI-Powered Log Entry Summary
AI-powered Log Entry Summary brings instant clarity to even the most complex log data. By translating raw log lines into a simple “who, what, when, where, and why” framework, analysts can quickly uncover insights without needing to interpret vendor-specific syntax or business logic. This removes the cognitive burden from investigations and hunts, allowing teams to spot threats faster across all data sources. Teams benefit from accelerated triage, more efficient investigations, and smarter decisions driven by clear, actionable context.
Exposure management
Cloud Runtime Security (application detection and response)
Earlier this year, we made a significant announcement that Rapid7 had partnered with ARMO to add AI-powered cloud application detection and response (CADR) – or cloud runtime security – to our cloud security portfolio. We are thrilled to announce that these capabilities are now integrated with Rapid7 Exposure Command Ultimate. For our customers, this milestone represents our ability to deliver on the promise of a complete cloud-native application protection platform (CNAPP) that helps security teams preemptively identify and proactively thwart attacks. If you’re interested in learning more about this latest innovation to our cloud security portfolio, reach out to one of our account executives.
Top Remediation Report in Remediation Hub
Understanding which remediations to prioritize is only part of the process, teams also need asset-level detail to act. Top Remediations Report adds that context in Remediation Hub, with customizable filters, shared visibility across teams, and automated scheduling for recurring delivery to key stakeholders in CSV, HTML, or PDF. The result is faster coordination, clearer ownership, and quicker remediation progress.
Remediation Bulk Export API
We understand that organizations need to customize reporting for various stakeholders and levels across their business to drive effective vulnerability remediation and communicate security posture. One of the ways that organizations address this need is through our powerful cloud-based API, which enables teams to extract and export large amounts of security data into external tools like Tableau or PowerBI. Customers can export security data at scale, including assets, vulnerabilities, remediations and agent-based policy data, resulting in more flexible reporting and querying.
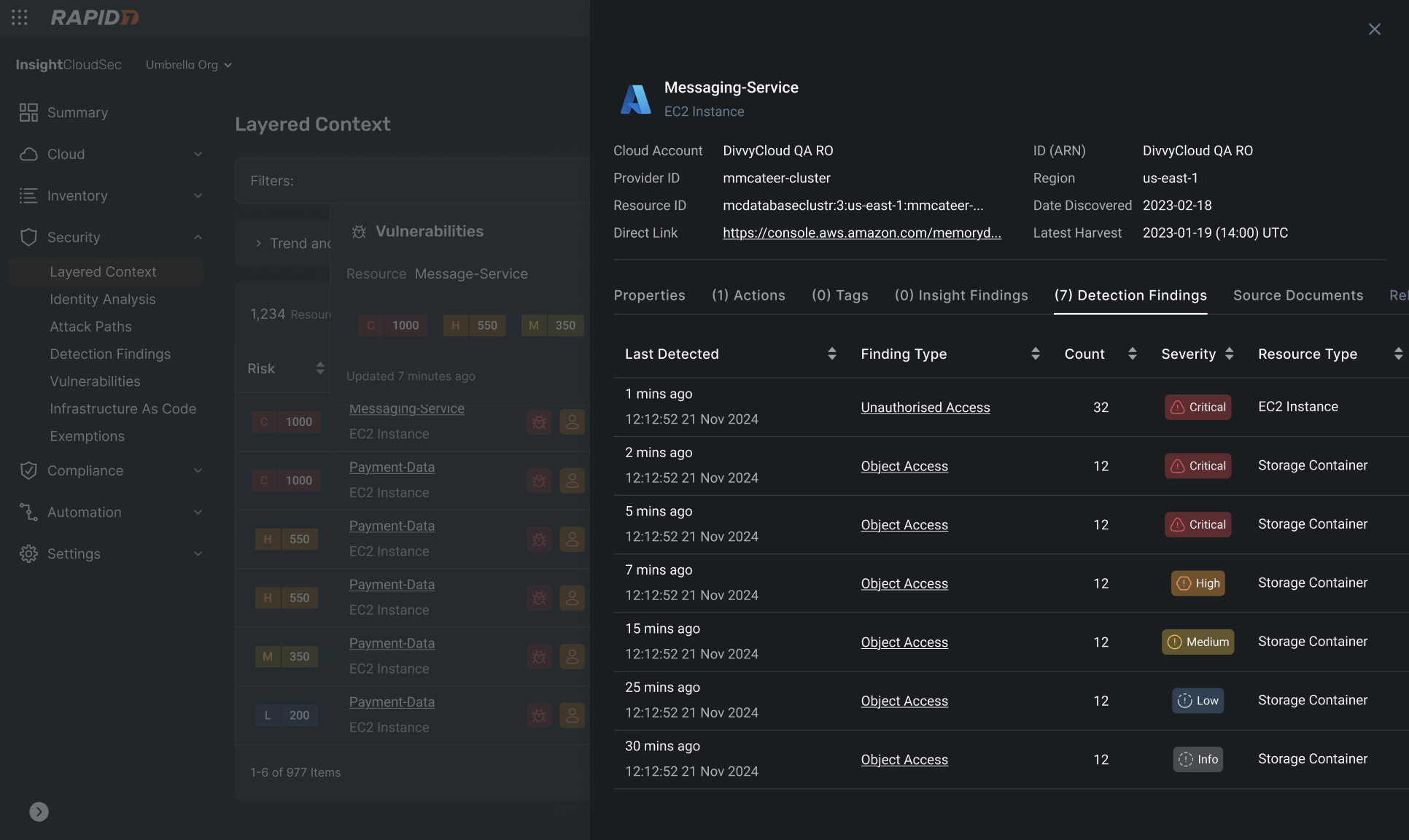
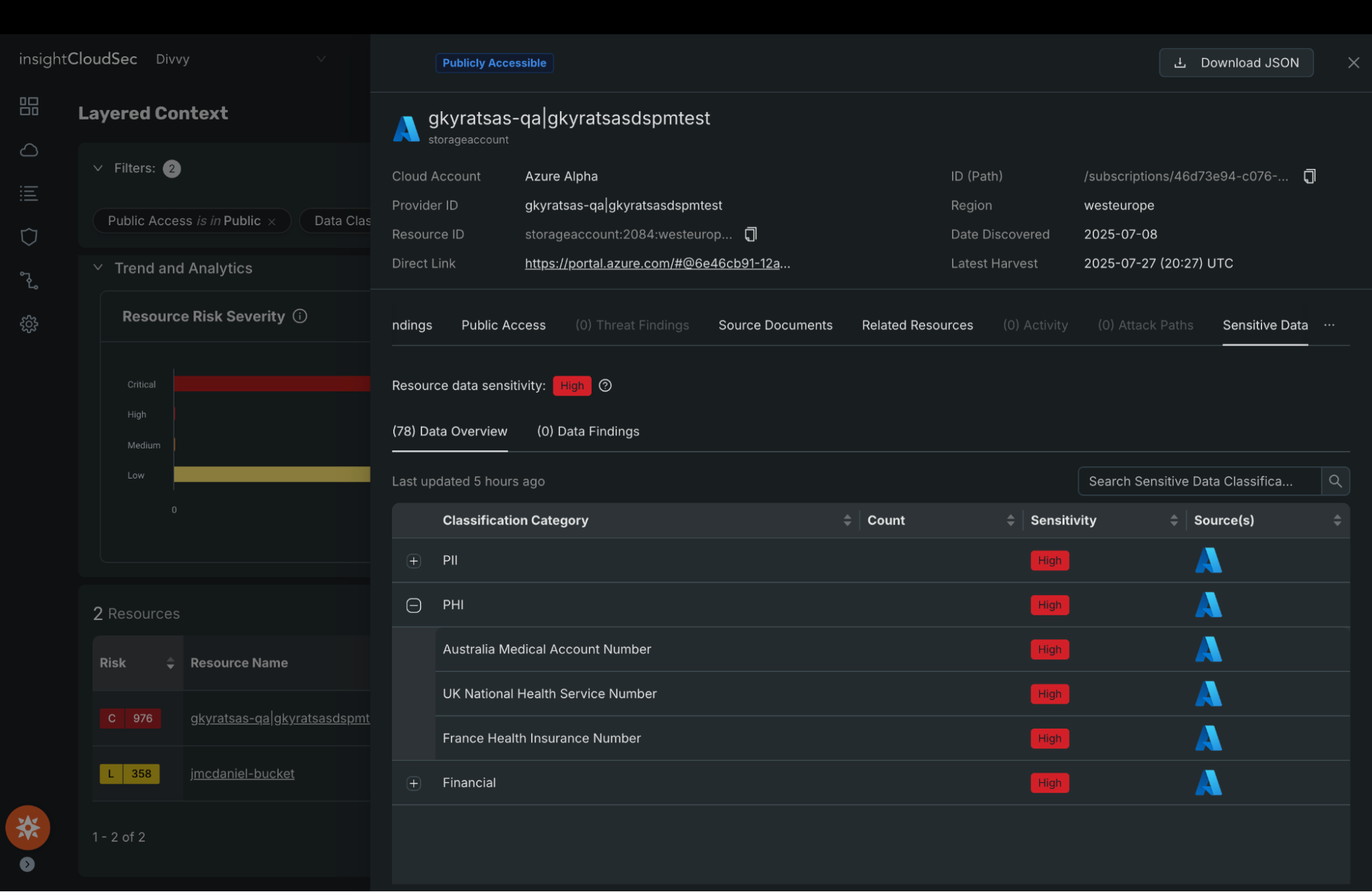
Data Security Posture Management (DSPM)
Understanding which exposures threaten sensitive data is difficult when data security and exposure insights live in separate tools. A partnership between Rapid7 and Symmetry Systems brings those perspectives together on Exposure Command, aligning sensitive data intelligence with real attacker reachability. DSPM capabilities discover sensitive data and map identity access, helping teams prioritize remediation based on breach impact.
Read the blog to learn how aligning data and exposure reduces breach risk.
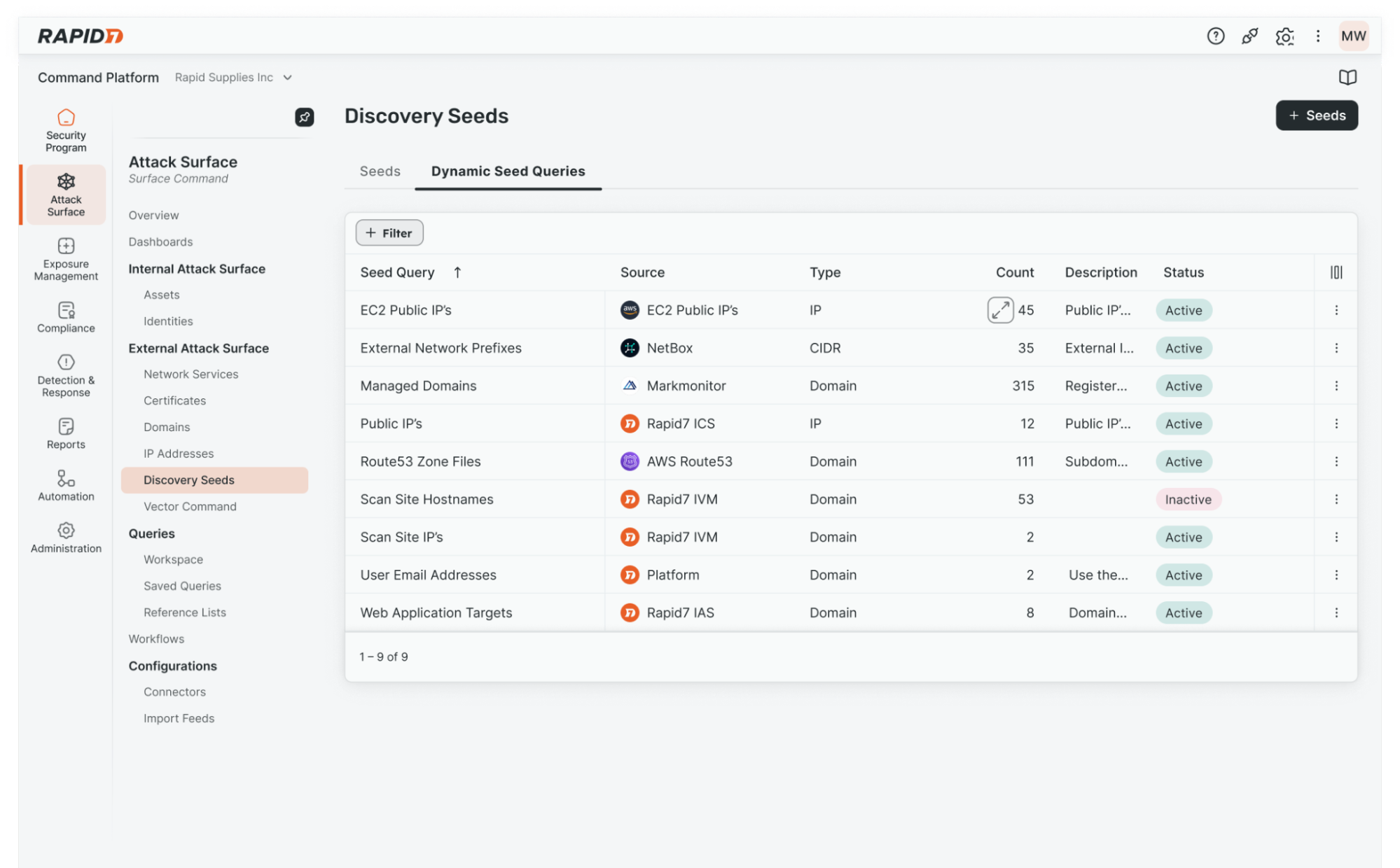
Attack surface management
Dynamic External Attack Surface Discovery
Your attack surface doesn’t stand still, and point-in-time visibility can leave teams chasing what’s already changed. Dynamic EASM Discovery helps Surface Command automatically identify and track changes across the external attack surface by ingesting domain and IP data from across the environment. The result is more current visibility, fewer blind spots, and stronger confidence that teams are prioritizing and validating the exposures that matter most.
Read the blog to see how Dynamic EASM Discovery helps teams keep pace with a changing attack surface.
Platform and Labs
Rapid7 Command Platform
We’re excited to introduce a centralized way to programmatically access data across all managed tenants with new multi-tenant API keys. For organizations managing multiple environments, tenants, or customers, integrating with each one individually has traditionally required significant manual effort, creating, maintaining, and rotating separate API keys for every tenant. This not only slows down development but also increases operational overhead and the risk of inconsistency.
With this new capability, you can build a single integration that seamlessly “loops” through tenants automatically, enabling consistent data access and streamlined workflows at scale. Whether you’re aggregating data for reporting, powering automation, or integrating with third-party tools, multi-tenant API keys simplify the process and reduce complexity, freeing up your teams to focus on higher-value tasks instead of repetitive configuration. Read all about it in our blog.
Rapid7 Labs
The latest threat research reports from Rapid7 Labs
This quarter Rapid7 Labs continued to deliver critical insights into the evolving threat landscape, uncovering how attackers are adapting their tactics – from stealthy, long-term intrusions to increasingly targeted and data-driven attacks. Our latest research reports highlight the growing complexity of modern threats and the real-world risks facing organizations today. Explore the findings below to better understand what’s changing and what it means for your security strategy.
BPFdoor in Telecom Networks: Sleeper Cells in the Backbone: Rapid7 uncovered a long-running espionage campaign in which a China-nexus threat actor, Red Menshen, embedded stealthy “sleeper cells” inside global telecommunications networks using the BPFdoor backdoor. Operating at the Linux kernel level, this malware enables persistent, hard-to-detect access without typical network signals, allowing attackers to monitor communications, subscriber data, and critical infrastructure over time. The research highlights a shift from opportunistic attacks to deliberate, long-term pre-positioning inside core systems that underpin global connectivity, raising national-level risk.
2026 Global Threat Landscape Report: The latest report from Rapid7 Labs delivers an in-depth analysis of global adversary behavior, drawing on telemetry from Rapid7 MDR investigations, vulnerability intelligence, and frontline incident response. This year’s findings highlight a rapidly evolving threat environment, marked by the collapse of the window between vulnerability disclosure and exploitation, the continued industrialization of ransomware operations, and the acceleration of modern attacks through the use of AI.
Executives’ Digital Footprints Threat Report: Today, 60% of an executive’s digital risk exposure is retrievable through surface web searches, including public records, professional history, and social media activity — all of which can be weaponized for highly targeted attacks. The Executive Digital Footprints Threat Report from Rapid7 Labs details how these executive digital footprints are an often overlooked threat vector that can be exploited, posing risks to the executive, their families, and organizations.
Exposing the Chrysalis Backdoor
Last month, Rapid7 uncovered the Chrysalis backdoor, a sophisticated supply chain attack that leveraged the Notepad++ update mechanism to selectively target organizations with a stealthy, persistent backdoor. This discovery highlights the growing risk of trusted software being weaponized and the real-world impact of advanced, targeted campaigns that can evade traditional defenses, reinforcing the importance of continuous monitoring and validating third-party software behavior in today’s threat landscape. Learn more about the Chrysalis backdoor here, and see more details on its impact and what you can do next here.
Cyber threat activity related to the Iran conflict
Rapid7 is actively monitoring cyber threat activity related to the Iran conflict, providing support for our customers and the cybersecurity community. Review observed activity, official advisories, and recommended defensive actions here.
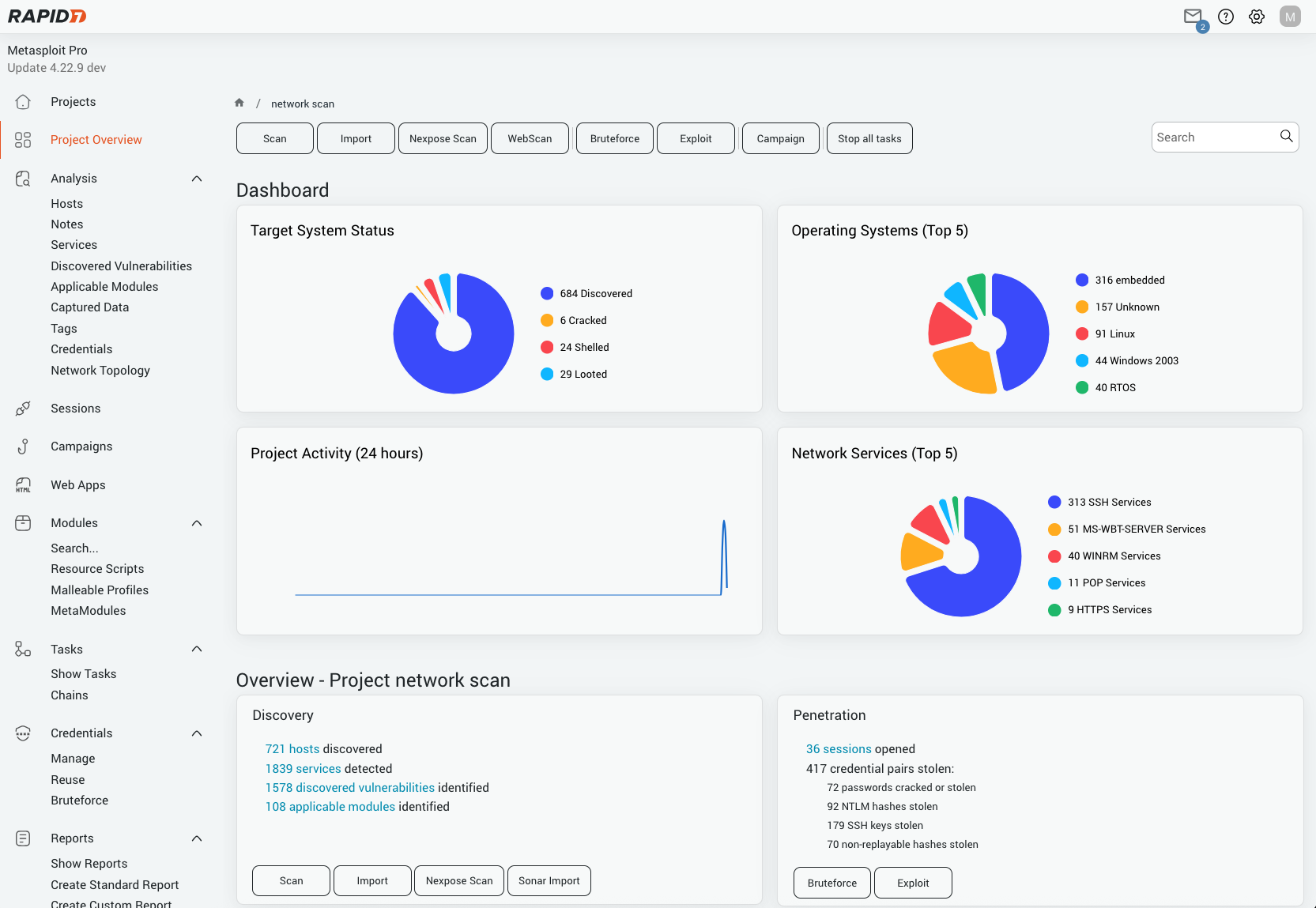
Announcing Metasploit Pro 5.0.0
We’re excited to announce the launch of Metasploit Pro 5.0.0, a major evolution in red-team and penetration testing. Built to address today’s dynamic threat landscape, this release delivers a significantly improved UI, usability, validation, and workflow improvements that empower security teams to validate vulnerabilities faster and more effectively. Learn more in our blog post here.
We’re just getting started
The innovation doesn’t stop here. We have a strong pipeline of product enhancements and new capabilities rolling out all year long. Be sure to follow our blog and release notes to see how Rapid7 continues to advance our platform and deliver greater value.
What’s New in Rapid7 Products and Services: Q1 2026 in Review
Source: Rapid7
Source Link: https://www.rapid7.com/blog/post/pt-whats-new-rapid7-products-services-q1-2026